The Myth of Automated "Deleted" Data
Why red numbers in a report require manual verification. Forensic software flags data as "deleted" based on database markers — but those markers can be inaccurate, and the underlying data may tell a very different story.
What the Red Numbers Actually Mean
When Cellebrite and similar tools display artifact counts in red, they are flagging data that the software has identified as potentially deleted or recovered from unallocated space. These numbers are not a reliable indicator of what data actually exists on the device — they reflect what the automated parser was able to interpret, not the full picture.
Critical distinction: A red number in a Cellebrite report does not confirm that data was deleted by the user. It means the software's parser flagged it — which may reflect a database marker, a file system artifact, or simply a parsing limitation. Manual verification is required before any forensic conclusion can be drawn.
Full Extraction vs. Discovery Export: A Side-by-Side Comparison
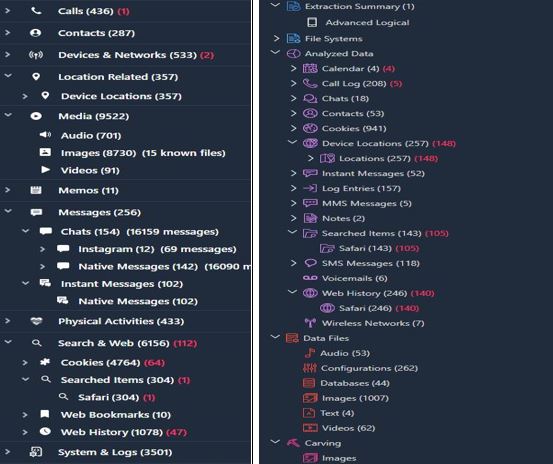
The comparison below shows the artifact tree from a full physical extraction (left) alongside the corresponding Cellebrite Reader discovery export (right). The red figures on the left represent data flagged by the tool — data that requires independent forensic analysis to properly characterize. Without that analysis, the prosecution's report presents an incomplete and potentially misleading account of what the device contained.
Note: the number of flagged deleted data is different in the original extraction compared to the Reader. This verifies the data is not the same.
Why This Matters for Your Case
Prosecutors frequently rely on the automated output of forensic tools without subjecting those outputs to independent scrutiny. When red-flagged data appears in a report, it is often presented as confirmation of deletion — implying consciousness of guilt or evidence tampering — without any verification of the underlying database structure.
A qualified forensic examiner can examine SQLite databases, inspect the actual deletion flags, review the timestamps, and determine whether the data was genuinely deleted by a user action, overwritten by a system process, or simply mischaracterized by the parsing software. That distinction can be the difference between inculpatory and exculpatory evidence.
Challenge the "Deleted Data" Narrative in Your Case
Forensic Cyber Investigations performs independent database-level analysis to verify whether flagged data was actually deleted — and by whom.
Call (702) 359-2500